A responsive CRM improves data security for nonprofits. Here’s how. Data is a catalyst in helping your nonprofit organization cultivate meaningful relationships with donors and make better decisions about fundraising. But maintaining data security for nonprofits is a big responsibility to take on, especially if you don’t have a reliable tool at your disposal. Follow along as we explain how a responsive nonprofit CRM can be your partner in creating a secure environment for your data. We’ll also explore key data features your CRM should come equipped with.
Data has become a growth tool for nonprofit organizations, elevating how they understand donor behavior, refine fundraising strategies, and measure the impact of their work. As organizations gain better access to data through advanced digital tools and analytics platforms, they bear an important responsibility: safeguarding their donor information from any cyber threats.
This requires organizations to take tactful security measures, such as ensuring compliance with data protection laws, fostering a culture of data privacy, and maintaining proper data hygiene practices within the organization. However, without a staff of IT experts who have a comprehensive understanding of these data security compliances and procedures, organizations have a hard time navigating the complexities of nonprofit cybersecurity, potentially creating open pockets to breaches and cyber attacks.
The Long-Term Implications of a Data Breach
If your organization is exposed to a data breach, it has immediate security repercussions and leads to more far-reaching consequences. Perhaps the most dire, this severely damages a nonprofit’s reputation in the community and erodes trust among donors, volunteers, and beneficiaries. The road to rebuilding trust and credibility could take years to recover from, leading to loss of support and an inability to make meaningful mission impact.
Equipped with a nonprofit CRM with built-in data security protections, your organization can mitigate these risks and properly safeguard your valuable donors’ sensitive information.
When exploring a new nonprofit CRM, thorough research and platform comparisons are mandatory. This ensures you select a solution equipped with the appropriate security measures for your organization’s needs. Neglecting to do so could expose your organization to risks, as even the most reputable platforms are susceptible to data breaches, evidenced by the recent case of Blackbaud, which faced significant consequences due to lax security measures.
“My organization was involved in [Blackbaud’s] data breach. That was a really huge thing for us with our board. We lost a lot of confidence in the way they handled that,” says Barbara Krusko, Chief Development Officer at Arizona’s Children Association.
Bryan Fegley, Senior Director of Advancement at Dominican Friars, further explains, “That was the moment for our organization where we poked her head out of the trenches to see what was out there. [The data breach] was what started the snowball that turned into the avalanche for us to leave Blackbaud.”
A Responsive CRM Prioritizes Data Security for Nonprofits
Responsive fundraising places the donor at the heart of every fundraising decision. It fosters giving through a four-step framework: listen to their supporters, establish connections, propose next steps through personalized suggestions, and make improvements based on fundraising data.
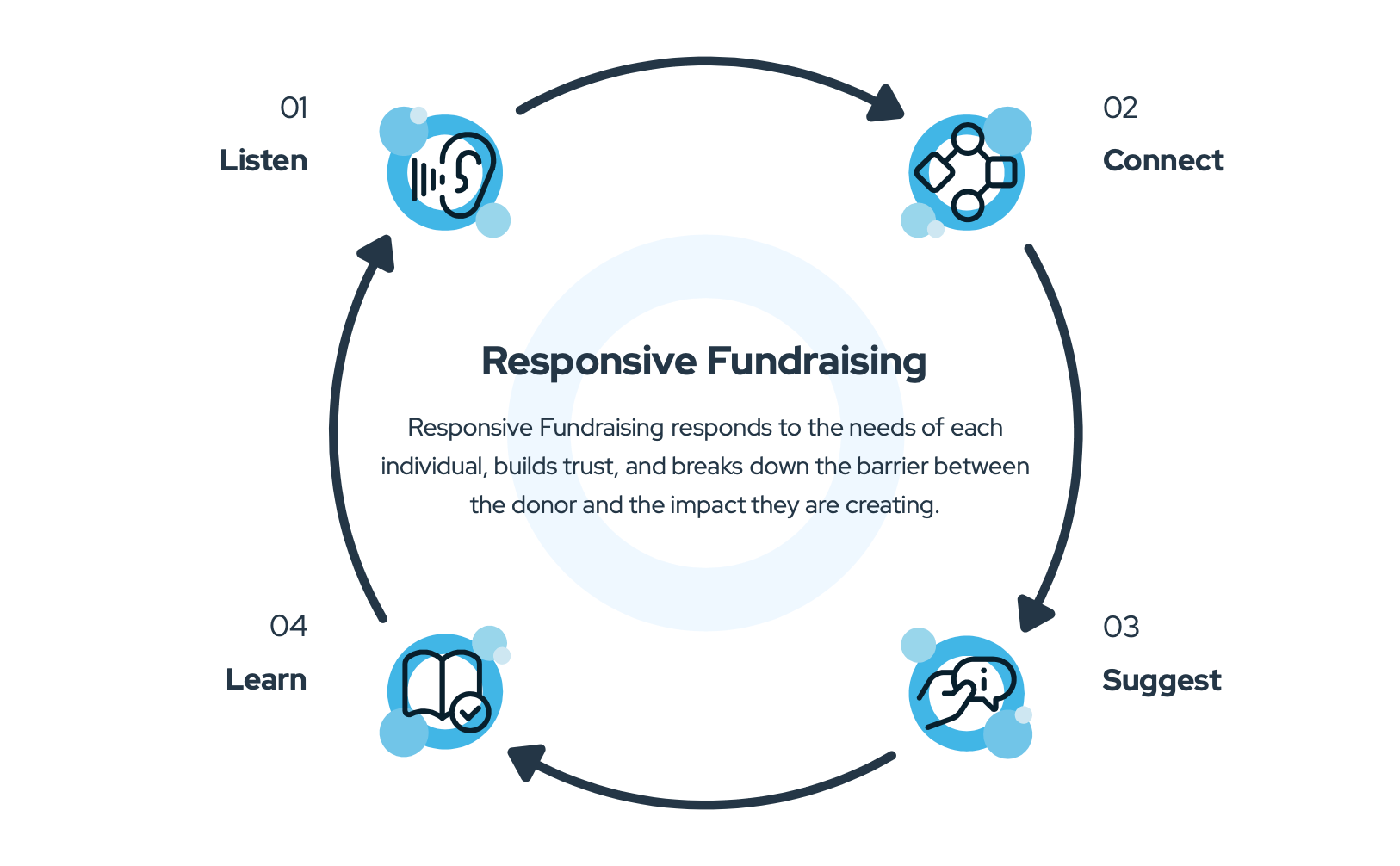
With responsive fundraising, nonprofits are refining their approaches by crafting personalized donor experiences tailored to each individual’s unique needs. This personalized approach fosters meaningful, lifelong connections with donors, driving deeper engagement and support. However, for responsive fundraising to truly be effective, it must start within the organization.
An organization-wide commitment to responsiveness ensures that donor needs and preferences are central to decision-making and strategy development. This principle extends to the careful selection of internal systems and processes, creating responsive external interactions and internal operations.
A responsive CRM like Virtuous continues to innovate its technology to address emerging cybersecurity threats, ensuring that your organization remains protected against potential breaches while delivering exceptional donor experiences.
The safety and security of our nonprofits’ donor data is our highest priority, so we run entirely on the Microsoft Azure Cloud Platform. Through Microsoft, our nonprofits rest at ease knowing their data is secure and protected with the use of various encryption methods, protocols, and algorithms.
10 Key Data Security Features to Look for in a Responsive Nonprofit CRM
When it comes to managing donor relationships and advancing your organization’s mission, a responsive CRM for nonprofits goes beyond just donor management software; it becomes a partner in making strides toward your mission. However, with a plethora of options available, finding the right CRM that meets your organization’s unique needs can feel daunting.
To streamline your search process, we’ve compiled a list of 10 key features to look for in a responsive nonprofit CRM. From robust data security measures to advanced fundraising functionalities, these features are essential for maximizing efficiency, engagement, and impact within your organization.
1. Data Encryption
Data encryption is the process of converting sensitive information into a secret code to prevent unauthorized access, much like translating a message into a secret language that only those with the key can understand.
This is especially important for nonprofits, as data encryption protects donor information, keeping confidential data secure throughout the process of transmission and storage. Data encryption is an added layer of protection and should be considered when looking for any new digital platform.
2. Multi-Factor Authentication
MFA is a security measure that requires users to provide two or more verification factors to gain access to a system. Typically, these factors include something the user knows (password), something the user has (security token), and something the user is (fingerprint or facial recognition).
For authentication, Virtuous employs a sophisticated password hashing algorithm, which securely hashes passwords in a one-way process. Additionally, our API leverages this hashing to generate a time-based expiring token, enhancing security for each session.
Recognizing the importance of layered security, we also offer Two-Factor Authentication (2FA) through Authy for clients who require an extra layer of protection. This 2FA system adds an extra verification step, significantly bolstering the security of client data and providing our customers with peace of mind that their sensitive information is handled with the highest level of security.
3. SOC 1, 2, and 3
System and Organization Controls (SOC) compliance is a security framework to help organizations maintain a high standard of control over their information systems and data. Achieving SOC compliance shows that an organization has implemented stringent rules and procedures to ensure the security, availability, processing integrity, and confidentiality of its systems and data.
There are three types of SOC reports, each serving a different purpose:
- SOC 1: Primarily focuses on financial reporting controls. This is a neccessity for organizations that handle the financial information of their clients.
- SOC 2: Designed to address controls relevant to security, availability, processing integrity, confidentiality, or privacy. This is particularly important for SaaS and cloud computing providers that store customer data.
- SOC 3: Similar to SOC 2 but provides a general report that can be freely distributed and is less detailed, often used for marketing purposes.
For nonprofits, adhering to SOC standards can build up donor trust, as it assures them that their personal and financial information is being handled with utmost care and responsibility. Understanding the differences between SOC 1, SOC 2, and SOC 3 is important for determining which compliance is most relevant to your organization’s needs and operations. Get in the weeds about the differences between each.
4. ISO
The International Organization for Standardization sets globally recognized standards for various industries and processes, including those about data security and management. For nonprofits, adhering to ISO standards, particularly those related to information security, such as ISO 27001, is a significant step towards ensuring the highest level of data protection.
Through Microsoft Azure, Virtuous maintains a wide range of ISO compliances, including ISO 27001 (information security management) and ISO 9001 (quality management system). By aligning with these global benchmarks, we’re committed to best practices in data security, risk management, and continuous improvement.
5. PCI DSS
The Payment Card Industry Data Security Standard ensures that companies that accept, process, store, or transmit credit card information do so in a secure environment. PCI compliance is a layer of protection against theft and fraud by having security requirements like encryption, access control, and network monitoring.
In Virtuous, all credit card and ACH processing is handled through our Virtuous Giving product, which is rigorously covered by our PCI scanning and auditing process. We partner with WePay as our Payment Gateway, which plays a critical role in tokenizing and encrypting all customer information, thereby ensuring the highest level of security.
6. GDPR
The General Data Protection Regulation sets guidelines for the collection and processing of personal information from individuals within the European Union. Organizations need to align with GDPR standards, regardless of where they are geographically located. This commitment not only ensures compliance but also reflects an organization’s dedication to protecting personal data and upholding the highest standards of privacy and security.
Virtuous supports GDPR compliance across our platform. Our commitment to data protection is further reinforced by our compliance with the Health Insurance Portability and Accountability Act.
7. HIPAA
The Health Insurance Portability and Accountability Act is a set of rules and regulations that govern the security and privacy of sensitive healthcare information. It’s a requirement that protects patient health information from unauthorized access, use, or disclosure.
Because we work with several healthcare organizations, we complete a comprehensive HIPAA risk assessment annually, looking at our platform and all the tech we use during data conversion and migration. This deep dive is our way of making sure we’re doing everything by the book, adhering to the strict requirements of HIPAA.
8. Security Audits
Security audits are like the health check-ups for any platform dealing with sensitive data, especially CRMs that nonprofits rely on. Regularly doing these security audits is important, as it helps your organization identify vulnerabilities or weaknesses in the system and processes.
This proactive approach allows for the immediate addressing of any issues, ensuring your organization is up-to-date with industry standards and regulatory requirements.
9. Data Backup and Security
Keeping your donor data safe is important and helps operations run smoothly. But let’s face it, sometimes things go wrong—like unexpected data loss. That’s why you need a solid backup and disaster recovery plan.
At Virtuous, we know how much you want to safeguard your donor data, which is why we have comprehensive backup and disaster recovery measures. Our system ensures that all customer data is backed up at the transactional level, offering up to 48 hours of data retention. On top of that, daily snapshots enable rollback to any previous point in time, providing peace of mind in the event of an unforeseen data incident.
For our enterprise customers, we go the extra mile by offering the option of SQL data for off-site backup upon request. This additional layer of protection further enhances data security and resilience, mitigating the impact of potential disasters.
With Virtuous, your organization can rest assured that your donor data is safe, secure, and resilient, allowing you to focus on what matters most—advancing your mission and driving positive change in the world.
10. Network Security
Network security involves a variety of measures and technologies, like firewalls and VPNs. While having the right technology in place helps, it’s also about policies and procedures that ensure safe and responsible use of the network. This includes regularly updating and patching software to fix any vulnerabilities, and training staff to be aware of potential security risks, like phishing attacks.
Through Microsoft Azure, Virtuous adopts an end-to-end zero trust strategy, which requires the verification of each request as if it comes from an external, uncontrolled network. The zero trust strategy follows three core principles:
- Explicit verification: We make sure to double-check every detail when it comes to authentication and authorization. This means looking at everything we can, including who the user is, where they are, the health of their device, what kind of work they’re doing, how sensitive the data is, and if anything seems out of the ordinary.
- Controlled access: We follow a policy of giving users only the access they need, exactly when they need it. This approach, known as Just-In-Time and Just-Enough-Access, along with adaptive policies based on risk assessment, helps us keep both our data and productivity safely in check.
- Preparation for breaches: We operate on the assumption that breaches can happen. Our strategy is to limit the impact of any breaches and stop them from spreading by carefully controlling who has access to what, depending on their network, role, device, and the applications they use. We make sure every single session is fully encrypted from start to finish and use analytics to keep an eye on things, spot any potential threats, and continuously beef up our defenses.
With Virtuous, you get a responsive nonprofit CRM that prioritizes your data security and ensures your organization is well-equipped to handle modern cyber threats. If you’re interested in seeing how our CRM can level up your nonprofit’s data security and donor management, schedule a chat with one of our team members.